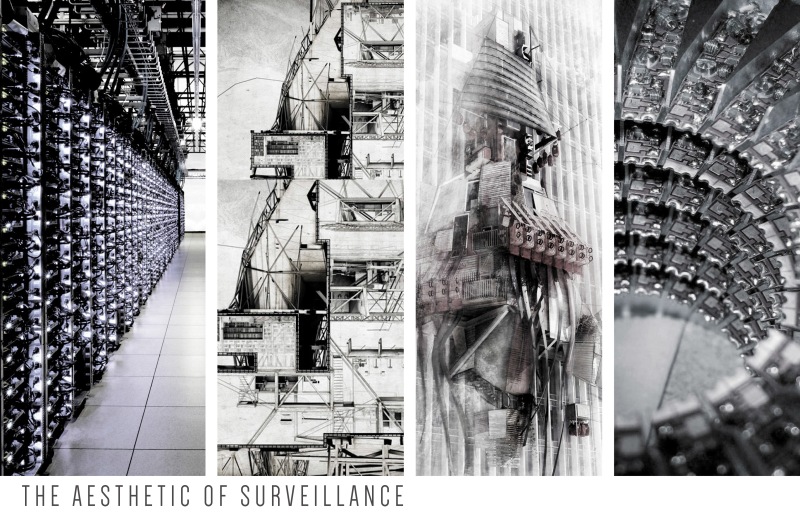
Surveillance and detection concepts already in operation, or under development:
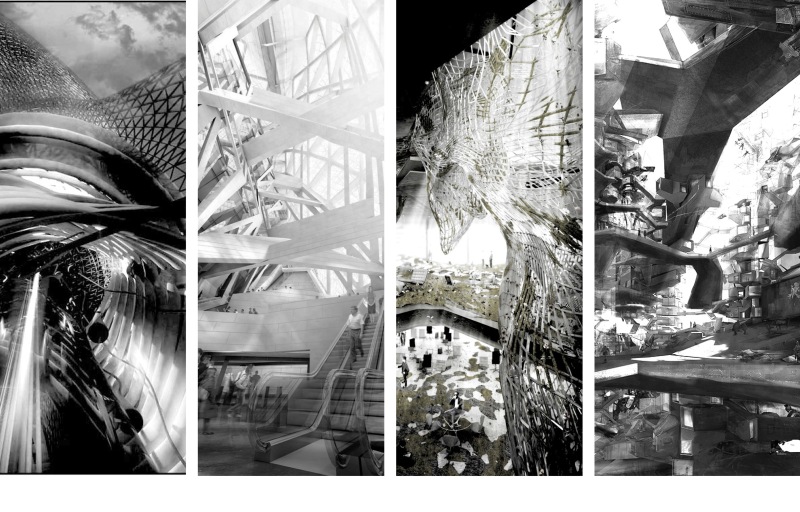
- A group of smaller surveillance drones called NAV (nano air vehicles) or MAV (micro air vehicles) already have been commissioned: mapleseed drones; sparrow drones by 2015, dragonfly drones to fly in swarms by 2030, and eventually a housefly drone. And if the reconstruction of nature doesn’t pan out, nature itself can be hijacked using electrical impulses to create cyborg surveillance insects being studied at major universities.
- Nano sensors for use in agriculture that measure crops and environmental conditions.
- Bomb-sniffing plants using rewired DNA to detect explosives and biological agents.
- “Smart Dust” motes that wirelessly transmit data on temperature, light, and movement (this can also be used in currency to track cash).
- Nano-based RFID barcodes that can be embedded into any material for tracking of all products . . . and people.
Hybrid Insect Micro-Electro-Mechanical Systems
Hybrid Insect Micro-Electro-Mechanical Systems is a project of DARPA, a unit of the United States Department of Defense, with the goal of developing tightly coupled machine–insectinterfaces by placing micro-mechanical systems inside the insects during the early stages of metamorphosis. The primary application is surveillance.
Remote controllable insects and their artificial robotic imitations are currently being promoted as covert spies. The development of tiny electronic control systems and miniature cameras has opened up a world of stealthy insect drones capable of slipping unobserved into military command and control centers
DARPA Minds Eye Program
The program’s focus is the development of smart cameras that can actually think for themselves. These systems will not just watch us but will also be able to analyze visual data-sets and assign significance to that data. The program’s focus is the development of smart cameras that can actually think for themselves. These systems will not just watch us but will also be able to analyze visual data-sets and assign significance to that data. via » DARPA Kicks Off Mind’s Eye Program Alex Jones’ Infowars: There’s a war on for your mind!.